> .\compile_stealth.exe --target WindowsDefender
Analyzing Static Signatures… [BYPASSED]
In Red Teaming, using unmodified public tools is synonymous with being detected. Security by obscurity does not work for defense, but it is vital for attack. Tools like RunasCs are instantly detected by static signatures. To evade this, we don’t need a 0-day, we just need to break the signature.
🔍 The Philosophy of Evasion Modern antiviruses (AV/EDR) look for known patterns. If your binary is named “RunasCs” and contains original text strings, it is a red flag.
“Code is not malicious because of what it does, but because of how it looks to the defender’s eyes.”
To transform a detected tool into an invisible threat, we apply three principles:
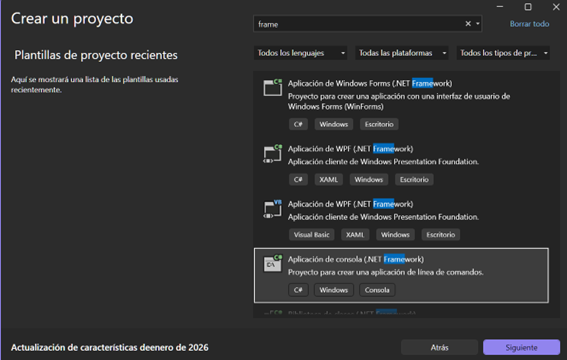
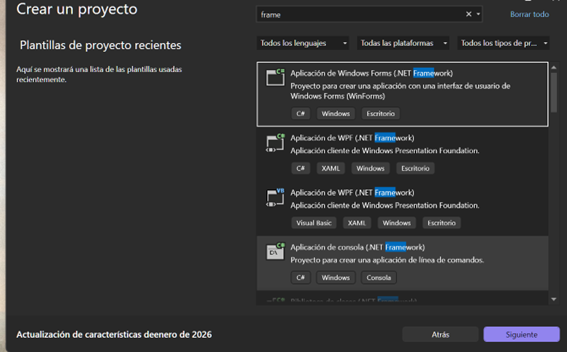
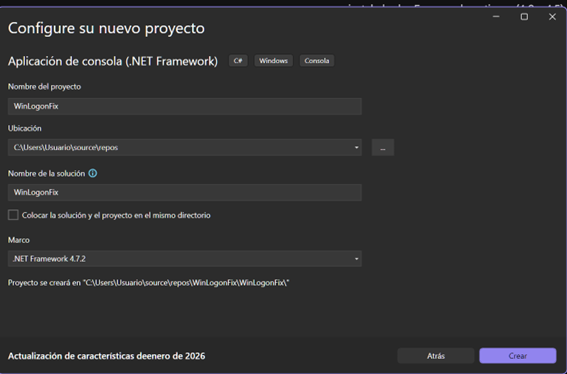
We create a new project in Visual Studio. It is vital to select Console App (.NET Framework) to ensure compatibility.
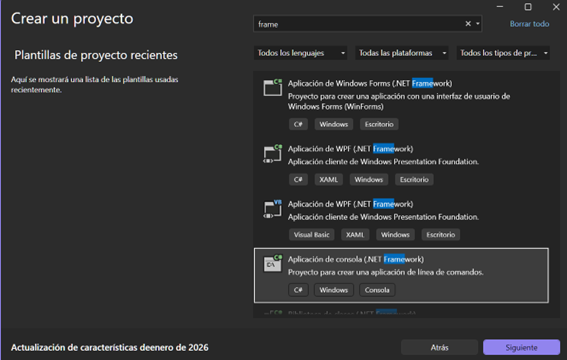
We give it a name that goes unnoticed in the system, such as WinLogonFix, and select Framework 4.7.2.
We delete the default code and paste the RunasCs source code.
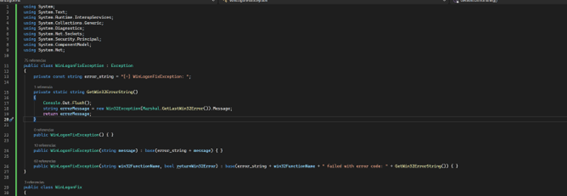
To avoid static detection, we use “Find and Replace” to change all references from RunasCs to WinLogonFix.
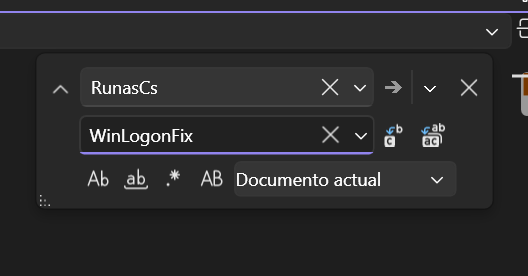
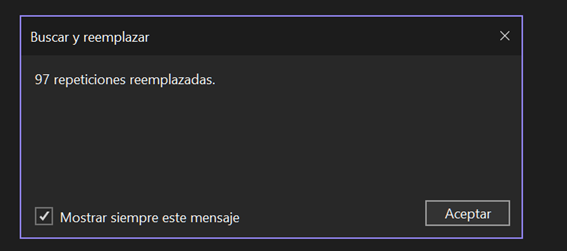
This modifies 97 references, breaking the antivirus’s basic signatures.
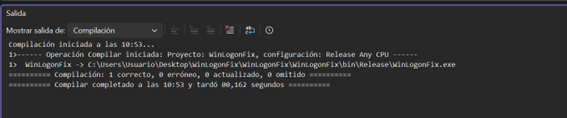
It is the moment of truth. We change the configuration from Debug to Release to clean the binary of unnecessary debug information.
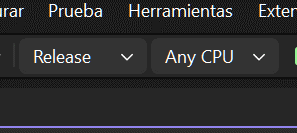
We compile the solution and verify that there are no errors.
To test it, we create a test user on our local machine:
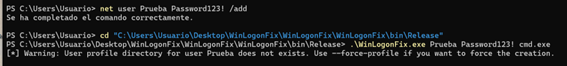
Finally, we execute the binary to launch a console (cmd.exe) as that user. As we can see, Windows Defender does not block it and we achieve successful execution (whoami).
I launched the attack to execute a whoami as that user:
.\WinLogonFix.exe Prueba Password123! "cmd.exe /c whoami"

Happy Hacking!